How effective are current Internet of Things authentications in response to security threats?
Overview of the Research
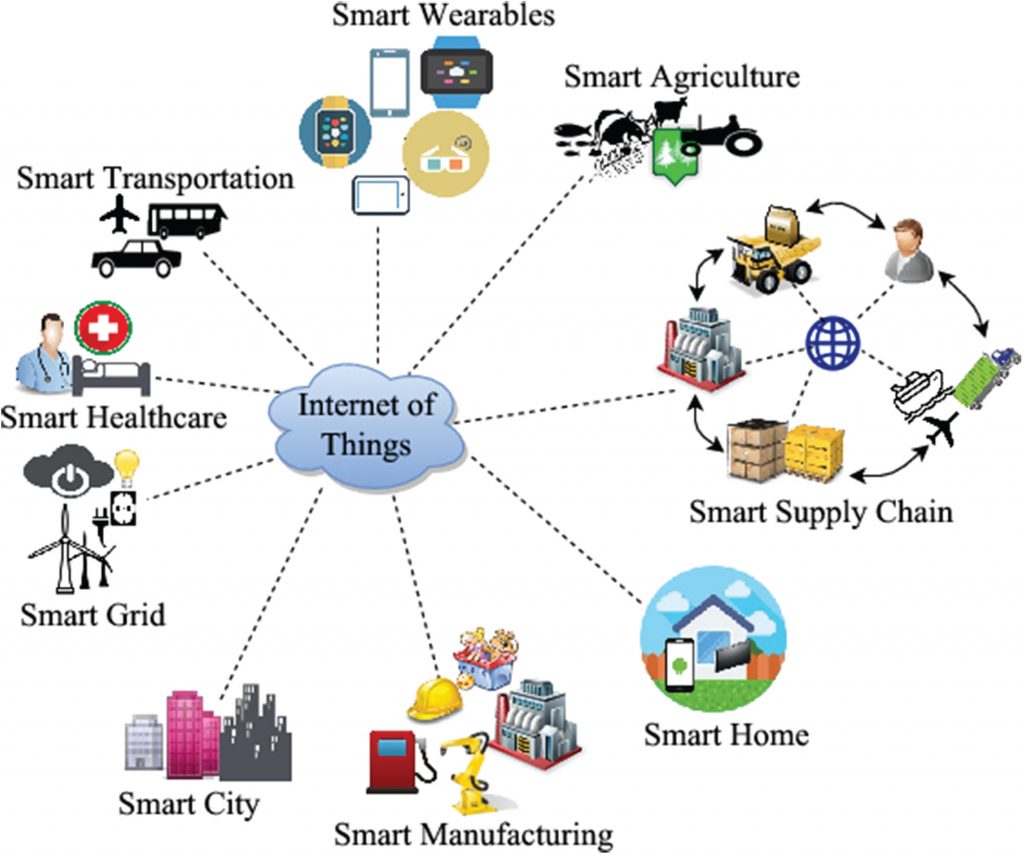
Security is a fundamental element in Internet of Things (IoT) and is considered a central theme in IoT Authentication process. Authentication is a process in which an entity’s identity is confirmed during login and additional information when signing-in such passwords, digital certificates, PIN; biometric and so forth are required. The IoT is a digital revolution that has eclipsed many technologies. The IoT has created viable potential for businesses and consumers enabling seamless transactions, however, it has also given rise to opportunities for hackers to engage in cybercrimes such as stealing personal information and intellectual property data and other fraudulent activities.Prevalent high-profile cyber security attacks such as Ashley Maddsion and TalkTalk sagas demonstrated vulnerabilities of IoT technologies. The IoT authentication encompasses several stages calibrated towards making data more secure while at the same time safeguarding the consumers’ right to privacy. In order to secure customers’ data from false IoT authentication is to resort to using biometric data. Other methods deployed in securing data is through incorporation of end-to-end encryption during data exchange process, which essentially renders data useless to those without authority to access and effectively prevents cybercriminals using data for ransom reasons.
Interconnectivity of networks in IoT brings along accessibility from anonymous and untrusted Internet that require novel security solutions. These have resulted into demand and consequent provision of security solutions. In the context of IoT authentication, authorisation credentials are required to access specific information within the expansive networks. Another example of IoT authentications is the concept of virtual keys. Strong IoT authentication such as encryption and securing managed encryption keys are important aspects in securing information that is stored by businesses and organisations.
The IoT software-based authentication is predominantly considered practical for its reliability. The current IoT authentication is based on passwords + OTP, however, this is still inherently weak. In this paper, this claim will be investigated. Towards this end, the paper discusses the implementation of a number of IoT authentications using cryptographic techniques based on symmetric keys such as public key cryptography and pre-shared keys in sensor nodes to provide End-to-End (E2E) within the context of data integrity and confidentiality. The Public Key Cryptography offers the best solutions in key management issues providing peer authentication without pre-shared secret on both ends. Furthermore, Public Key Cryptography provides additional services such as enhancement of IoT vision, in which symmetric key-based solution that is markedly limited in terms of service access on the basis of service type or group membership. However, Public Key Cryptography and other considerations will be evaluated in light of certificate-based IoT authentications making comparisons to pre-shared-key-based IoT authentication. Our improved IoT authentications deploying pre-shared-key approach will amortize certificate-based authentication high overheads through protocol extensions and offer robust and efficient protection against replay attacks.
In this paper, we propose to examine man-in-the-middle attack, denial of service (DoS) attack and replay attack. In other words, this paper poses the research question: How effective are current IoT authentications in response to security threats?In responding to this research question, this paper will discuss the current perspectives on IoT authentication protocols under the DoS, Man-in-the-middle, and replay attacks.
Motivation and goal
The need to improve authentication in IoT applications against DoS, Man-in-the-middle and Replay Attacks will remain the main goal of this study.
The Elliptic Curve Cryptography (ECC) [27] has been suggested as an efficient solution in Key generation while TinySec [28] is suggested as appropriate for symmetric encryption in IoT authentication process. However, some DoS, Man-in-the-Middle and Replay attacks can disrupt and pose security threats to this proposed solution. Consequently, from the foregoing, current IoT authentication process lacks a strong end-to-end encryption and based on this inadequacy inherent in existing solutions;our proposal for conducting a research was motivated by the need to developa strong IoT authentication. Some earlier IoT authentication solutions that have been implemented are obsolete against emerging cybercrimes and require further improvements, standardization and refinement. In order to realise the full potential inherent in IoT technology, will mean going beyond current IoT authentications against DoS, Man-in-the-Middle and Replay attacks and implementing one common solution for IoT authentication to enable seamless flow of information between users [29]. This will then enable user-centric IoT authentication guaranteeing information flows and generation of new services that are of high value to society.
Aim and objectives
The aim of this proposal is to research into IoT authentications proposed and develop a novel common solution against DoS, Man-in-the-Middle and Replay attacks.
The following are research objectives identified:
- Examine various IoT authentication protocols against DoS, Man-in-the-Middle and Replay attacks in heterogeneousIoT authentication scenarios and obtain current references to the State-of-the-art (SOA) status of IoT authentication technology
- Develop a novel IoT authentication protocol against DoS, Man-in-the-Middle and Replay attacks to ensure privacy, information security and data protection.
- Discuss and determine the weaknesses of proposed IoT authentication protocol, if any.
Challenges
The IoT authentication faces various vulnerabilities and these remains the main issue in providing security in many applications. The current IoT authentication is limited in providing security to only one particular threat such as DoS, Man-in-the-Middle or Replay attacks. IoT authentication is used in providing security to many applications using cryptography, public key cryptography and many others.
Information security has been a major concern in IoT authentications due to the prevalence of applications that are potentially risky because of their natural multiplicity of collecting data of individuals in IoT environment. For example, the implementation of contactless-credit cards that permit card number and name to be read without IoT authentication makes it possible for cyber criminals to purchase goods using bank account number of card holder and identity.
In view of IoT authentications challenges, main objectives of the current IoT authentications are effective protection of personal data and effective information security entailing confidentiality and integrity.
Cryptography has been used over the years in providing effective defense against security loopholes in many applications with varying success because of increasing nature of attacks. In essence, this means that effective defensive against these attacks using one security application is not possible without having different layers of security against these three threats to IoT authentications.
Therefore, our mainobjective will be to provide an IoT authentication that provides security against these three threats using an improved IoT authentication approach to guarantee near-total security as a countermeasure in defeating security threats posed by denial of service, man-in-the-middle and replay attacks.
Positioning of the Research
The current security models for IoT authentications are constrained by various emerging factors. The most important constraintis that IoT applications that foresee participation of many nodes can pose serious security concerns. There are many attacks that are more likely to occur in IoT such as Denial of Service (DoS), replay attacks and Man-in-the-middle as proposed by [1]. Among the latest attacks related to IoT was an attack against Supervisory Control and Data Acquisition (SCADA) systems [2]. The use of commercially available cloud computing technology, has led to increased IoT technology relying on SCADA systems. However, there have been several security vulnerabilities that make it possible to launch attacks on these systems such as Denial of Service (DoS) [2]. Therefore, many challenging security limitations must be addressed through IoT authentications.
In the recent decades, there have been studies revealing research activities in IoT authentications [3, 4, 5, 6, 7, 8]. However, these studies mainly focused on IoT models with security and privacy being treated as one integrated concept. A study of applications relating to IoTauthentications were proposed in areas such as logistics, healthcare, transportation, personal, smart environment and social domains [3]. The authors focused on IoT authentications and data integrity issues and proposed a number of research directions for issues such as man-in-the-middle attack [3]. In relation to privacy issues pertaining to IoT applications, the authors proposed the development of new software application that has capability of controlling access to personal information. However, the survey fails to provide adequate details regarding security challenges in IoT authentications. In a related study [5], the authors failed granting adequate attention to IoT authentication.
In another study, the authors presented a cloud-centred vision for IoT authentications by illustrating enabling applications and proposed research issues[9]. In a related study, IoT authentication was revisited with the authors pointing out the limitations such as taxonomy of IoT authentication that remained unclear [10]. It was made clear that the aforementioned studies failed to consider security in IoT authentications as a priority and often revealed limited focus on IoT authentication issues. The intent of this paper is to offer supplementary effort in IoT authentications with the aim of improving IoT authentication security features. Towards this end, a systemic approach to improvingIoT authentication protocol is proposed.
The capabilities inherent in EPCglobal Class-1 Generation, cryptographic primitives and other related ultra-lightweightflexible solutions are among a class of IoT authentication to be considered. A public key algorithm involves using public key and a matching private key in ensuring security services inIoT authentication. The main merit of public key cryptography is non-requirement of preceding secret exchange between parties involved. However, conventional public key cryptography algorithm such as RSA requires high processing capability and long keys in ensuring a good security level. However, RSA operates only on long keys and large numbers in delivering sufficient security. In IoT authentications, we propose the alternative public key cryptography schemes having shorter keys such as Elliptic Curve Cryptography (ECC) and Hyper-Elliptic Curve Cryptography (HECC) [11]. A suitable alternative for improving IoT authentication is the combination of asymmetric encryption (Passerine), symmetric encryption (Hummingbird-2) and authentication code [26].
The Man-in-the-middle attack is prevalent in many IoT applications in which a third party adversary hijacks communication channel to spoof identities of two genuine nodes (N1 and N2) that are involved in network exchange and can either pass N1 for N2 and vice versa. In other words, the adversary can take control of communication channels between N1 and N2. This enables the adversary to intercept, send, modify, and discard any of the packets they want or replace or change target victim’s communication traffic. If, for instance, an individual was trying to make a withdrawal from bank account, the adversary can identify critical message, modify bank account details, and replay modified message. Man-in-the-middle attack will effectively make the bank server to recognise the transaction as a valid event since the adversary does not require knowing the identity of the supposed victim.
According to Conti et al. in [12], man-in-the-middle attacks take three diverse forms, namely: attacks based on impersonation techniques; attacks based on communication channel and attacks based on adversary’s location.There are several IoT authentication protocols that can be deployed to detect and avoid man-in-the-middle attacks. However, four IoT authentication protocols presented in various studies [13, 14, 15, 16] are based on mutual IoT authentication. With protocol [17], all the packets are encrypted with receiver’s public key cryptography making it possible to prevent man-in-the-middle attacks.
The Replay attack is similar to man-in-the-middle attacks in which adversary intercepts data packets and retransmits them without any decryption to destination server. Under this type of attack, the adversary may obtain similar rights as a genuine user. According to [18], replay attacks have been described as existing flaw in software or an application that will make it possible for an adversary to bypass authentication by replaying to the server similar message as original message. In bypassing IoT authentication through sniffing for the hashed passwords and then replaying same passwords to the server while encrypted as exemplified in CVE-2007-4961 and CVE-2005-3435.
However, there are IoT authentication protocols that are capable of detecting and avoiding Replay attack [19, 20, 21, 22, 23]. These IoT authentication protocols deploy Timestamp, Random numbers and Hash function. The random number approach is used by [20, 19] and [21]. The hash function uses protocols [22], which include IPSec protocols that implement an anti-replay mechanisms based on the Message Authentication Code [24].
The IoT authentication protocols belong to three categories namely symmetric-cryptosystem, asymmetric-cryptosystem and hybrid. Majority of the IoT authentication protocols deploy secure cryptographic hash functions [25]. Authentication is a crucial component when considering a design of a secure communication channel in IoT authentication [1], however, the provision of distributed, lightweight flexible solution that is resistant to attacks and ensuring comprehensive security for IoT remain the biggest challenge.
A novel solution was proposed by[1] and evaluated based on its capability in dealing with DoS, replay and man-in-the-middle attacks. These three attacks range from application based, connection based or platform based attacks and remain the most challenging in IoT authentications. Strategically, there is need in focussing on IoT authentication issues to provide the most holistic solution to improve IoTauthentications against DoS, Man-in-the-middle and Replay attacks.
Research Design and Methodology
Limitations in terms of practical resources to enable a fully-fledged testing of the challenges facing IoT authentications such as DoS, Man-in-the-Middle attacks motivated us to resort to desktop review of this issue. A desktop reviewing of the previous attacks will provide an entry point in understanding the concept of IoT authentications and developing it into reliable research concept.
The first step will be to identify background information by going through selected articles on IoT authentications. The articles will cover recent work done on IoT authentication and will be selected using various search criteria. The research design and methodology that will be employed in this research will be justified by the requirement of gaining preliminary overview of the studies undertaken previously in regard to inherent attacks in IoT authentications protocols. Reviewing of the work done within this field will be done using qualitative methodology. Sampling articles using a specific search inclusion and exclusion criteria from journal databases will be done. Journal articles on IoT authentication will be included in the study if they include key words such as IoT authentication, denial of service, man-in-the-middle and replay attacks. Potential articles will be excluded if they do not have the specified key words.
Sixty-five journal articles will be included in this study based on a sample of convenience. In addition inclusion criteria will be: peer-reviewed articles; at least not more than twenty years old from the date of publications. Exclusion criteria will be: journal articles not related to IoT authentication protocols; more than 20 years old and journal articles from sources without complete published results.
We will review background information from various literatures on IoT authentication and protocols and we will also use our own experience in IoT authentication derived from the studies. Peer-reviewed journal articles on IoT authentication will be used as the basis of getting background information on IoT authentication. The review of journal articles will be undertaken in three phases. In the first phase, a pool of possible selected journal articles identified from a broad-based search will be classified according to year when they were published. In the second phase, these will be narrowed down to only those reflecting IoT authentication protocols, DoS, man-in-the-middle and replay attacks. In the third phase, the journal articles will be evaluated based on their suitability for the study.
Data sources will be mainly electronic databases such as IEEE publications. Other sources will include reference lists from articles identified and conference proceedings as well as communication with other researchers and leading authors of published work. Search strategy will follow standardized formats that will be designed for IEEE journal articles and adapted for all other databases. We will construct the search strategy to be followed and which will be appended as an appendix in the final thesis. We will also hand-search reference lists to obtain further information in respect of IoT authentications once relevant articles for inclusion have been selected. Full publications will be obtained and reviewed.
Conclusion
The IoT highlights potentiality inherent in network capabilities while at the same time raises fears associated with such an emerging elastic technology. The future capabilities of IoT could be under security threats emanating from their deployment. The security concerns that have been dealt in this paper in regard to IoT authentications are DoS, Man-in-the-Middle and Replay attacks. Without addressing these security threats to IoT authentications through improved IoT authentications will limit the usefulness of IoTtechnology to society.
In addition, work related to IoT authentications have been discussed, including solutions for these problems using public key cryptography by weighing in the merits and demerits for each of the current IoT authentication solutions.After in-depth analysis of IoT authentication challenges and evaluation of existing IoT authentication protocols and examining their reliability and effectiveness against DoS, Man-in-the-middle and replay attacks, it is proposed that an effective common improved IoT authentication protocol to mitigate against security attacks be developed. It is anticipated that this research will provide a holistic approach to challenges in IoT and that the findings will help improve IoTauthentication against DoS, Man-in-the-middle and Replay Attacks.